TimeKeeper Compliance overview
Compliance builds on TimeKeeper Server on Linux to provide analysis and reporting for precision time networks for regulatory and data governance.
As events occur on your network, TimeKeeper reports them as needed, whether through syslog, Windows event log, SNMP traps, emails, and so on. As issues occur you get immediate notification however you need.
Compliance extends this capability by reviewing all of your time sources and servers over time and building custom reports based on their behavior. Audits are generated based on custom criteria on a daily, weekly, monthly, and yearly basis. Different groups of systems can be reported on independently, according to different warning and error thresholds based on different reporting requirements.
PDFs are automatically generated for all of these audits for easy reporting and quick display within the Compliance GUI within TimeKeeper. The data used for the reports is stored in a SQL-compliant database that is queryable, allowing for custom reporting if needed. TimeKeeper Compliance tracks a wide variety of clients using PTP, NTP, and other sources to provide timing statistics enterprise wide, all collected and reported from a common platform and interface.
Compliance benefits include:
- Enterprise reporting for precision time networks
- Enhanced analytical tools
- Custom reporting based on different hosts and reporting requirements
- Auditable daily/monthly/weekly/yearly reporting
- SQL interface, Excel export capability, automatic PDF generation
- Data governance
The product is enabled by license and option. To enable it first acquire a Compliance license from FSMLabs, then select the “Enable Compliance” option in TimeKeeper’s Configuration tab.
Your TimeKeeper Compliance package must be configured to receive and respond to management queries and must have active clients or be configured as a PTP client of an active TimeKeeper Server. All clients visible to the TimeKeeper instance will be visible to Compliance. For information on configuring TimeKeeper as a Client or Server, please see the “Configuration” section.
For historical data, historical files must be present. Please allow adequate time for reports to become visible as analysis ends at the end of the most recent hour.
Installation and operating system dependencies
The TimeKeeper Compliance reporting tool is part of TimeKeeper itself. So an installation of TimeKeeper will include the Compliance tool as long as the license enables it. This way no additional software or installations are needed.
Compliance does require some features from the host operating system before it is able to generate reports. Most notably are the font packages used. Those can be installed on most Red Hat/CentOS variants with:
yum -y install fontconfig libXrender libXext '*xorg*font*'
and on Ubuntu systems with:
apt-get -y install libxrender
apt-get -y install libxrender1 libfontconfig1
Enabling Compliance
Compliance is enabled or disabled via the GUI by selecting the Configuration tab and selecting the “Enable Compliance” checkbox, on a system with a Compliance-enabled TimeKeeper license. We’ll cover the specifics of this in the next section.
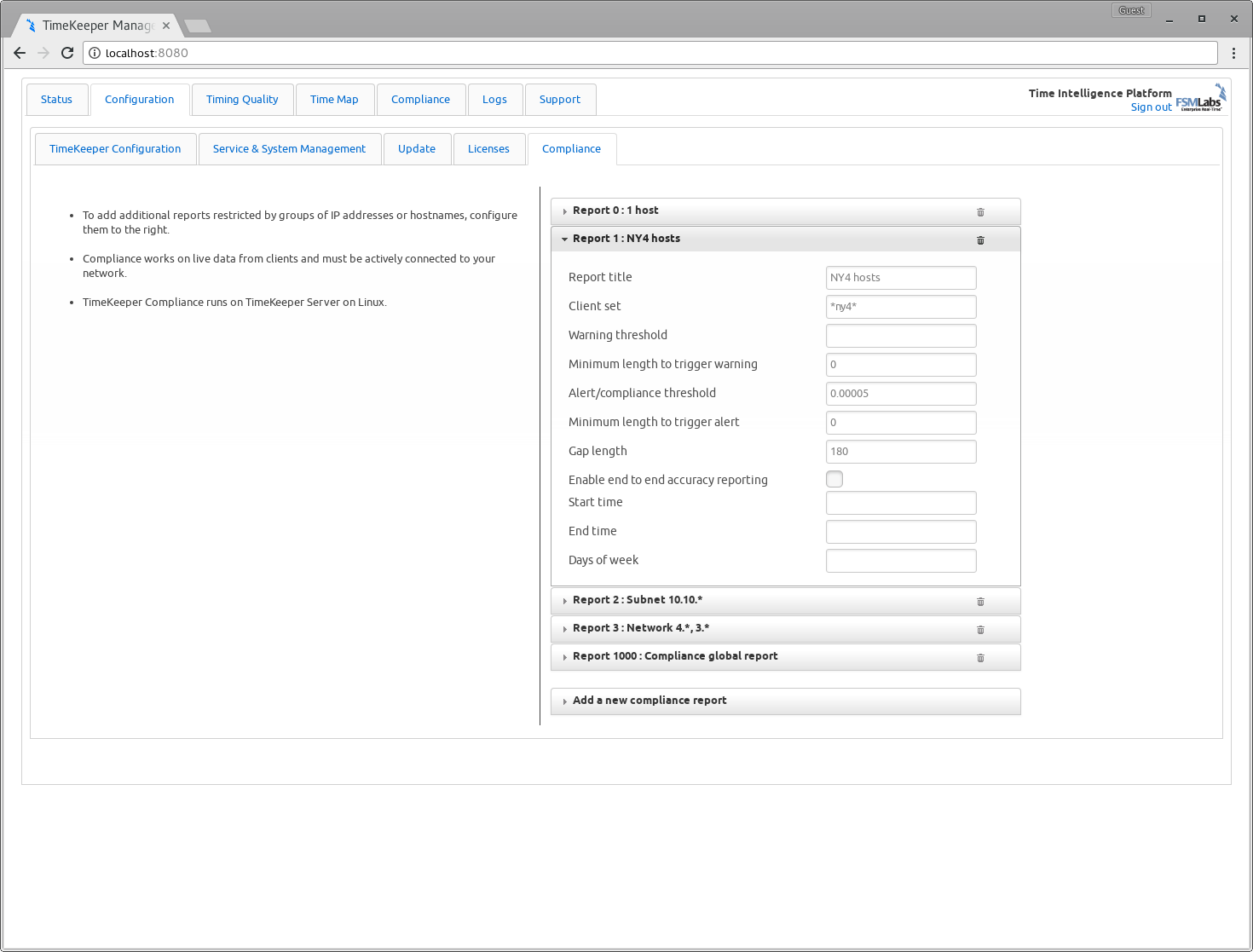
Once enabled, multiple reports can be configured, each for different groups of hosts subject to different alerting and reporting thresholds. Configured via the GUI, reporting configured like this:
Would automatically generate daily audits that look like this:
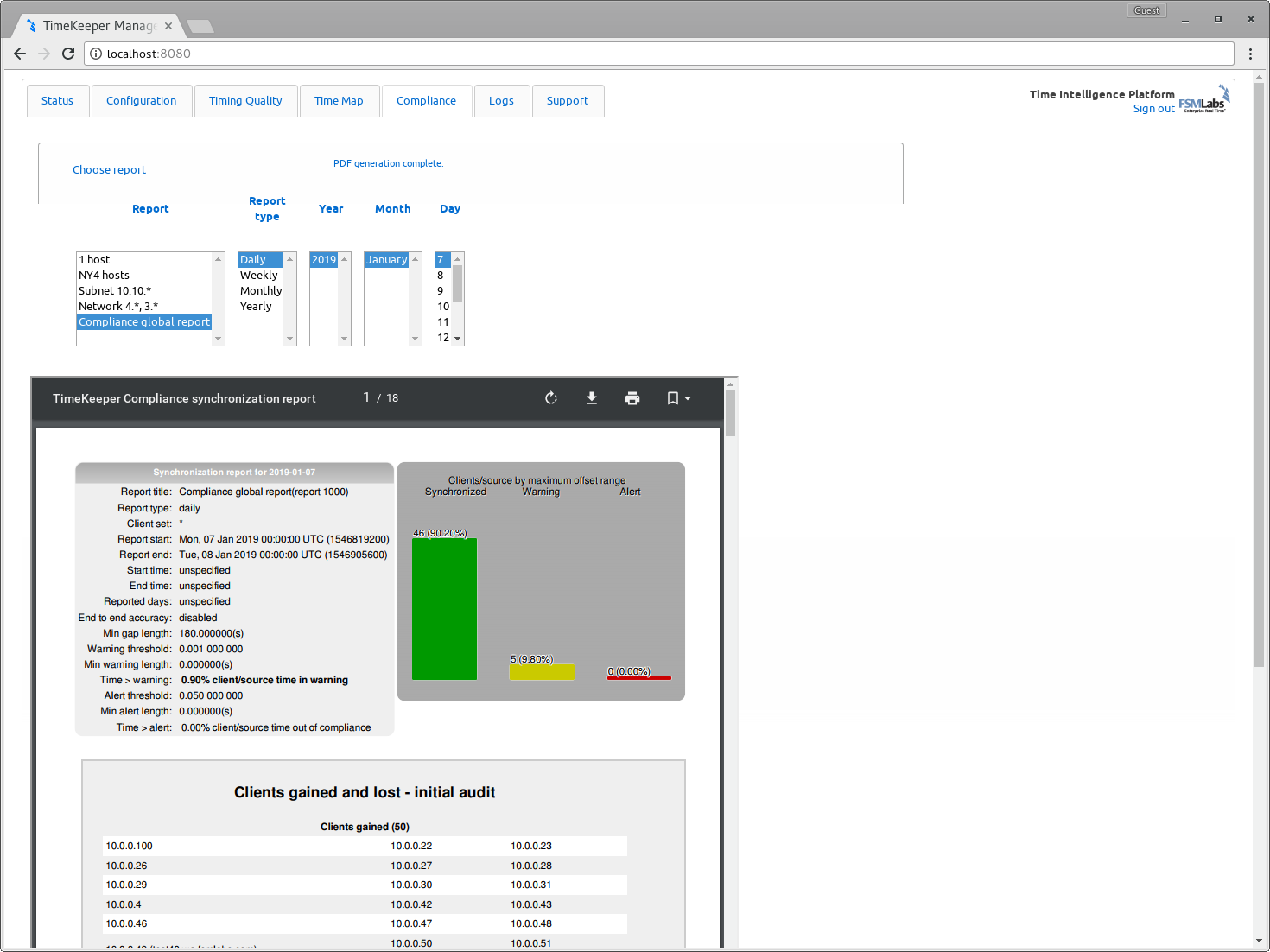
Looking at the sample in the window above, the audit is a PDF delivered inside the browser, and is also available for download. At the top of the PDF on the left is an overview of the audit configuration including details and client data that were used at the time that the audit was generated. On the right is a simple histogram indicating which clients were in sync, warning, and alert for the time period of the audit. Note that clients may be reported as being in both warning and alert depending on the events the clients generated.
In the next section, we’ll work through the specific configuration steps needed to set up Compliance and use it similar to what’s shown above.